I’ve had a lot of questions about DDoS attacks from customers recently—not just about the technical aspect of mitigating them, but more general questions about the whys and hows.
DoS stands for “Denial of Service.” DoS attacks are attacks whose outcome is intended to be preventing a service (e.g., a website) from doing its job. The first D in DDoS stands for “distributed,” which speaks to how the attack is performed, i.e., from a bunch of different places at the same time.
A DDoS attack is a crime in most countries. In the U.S., for example, they can be prosecuted under the Computer Fraud and Abuse Act of 1986, and in the UK under the Computer Misuse Act 1990.
This is a simple question with a complicated, and somewhat subjective, answer.
- DoS attacks are an instrument of digital warfare. Well-funded and well-organized groups of “hackers,” which are sometimes called “Advanced Persistent Threats (APTs),” use them as part of their campaigns to disrupt or disable their enemy. In these cases, infrastructure or communications are often targeted.
- “Hacktivisim,” using cyber attacks to further a social or political agenda, is common. In hacktivism situations, the attackers are often more vocal about the attack and its reasons, e.g., via social media.
- Sometimes a DoS attack is one part of a coordinated, sophisticated attack - maybe it’s a distraction, or maybe it’s to impair a particular subsystem to expose a vulnerability that it protects.
- Finally, and most frustratingly, attacks can happen for no clear reason at all. Attackers may have a personal vendetta, may be honing their skills, or simply enjoy the chaos.
Yes, they definitely are. From 2013 to 2022 there was something like an 800% increase in the number of DDoS attacks worldwide. One study says that Q1 2023 saw 47% more attacks than the same time period a year prior.
Probably because it keeps getting easier. Here’s a scenario. (As usual, it’s not like the movies.)
- Somebody, using a series of tactics we’ll discuss in a different article, gathers a collection of devices (personal computers, internet-connected thermostats, virtual machines in the cloud) that they have compromised (hacked).
- They link all of these devices together, so that they can instruct them all at once. This linking-together is sometimes called “command and control.” The swarm of compromised devices is sometimes called a “botnet.”
- The botnet owner puts access to their command and control up for rent, probably on a dark web site and payable in cryptocurrency.
- A bad actor, even (especially) one with limited technical know-how and/or modest means, rents the botnet for a few hours, and uses it to attack their target.
The bar is very low and the associated risk (because of the anonymity of the “dark web” and in cryptocurrency) is also low, so there really doesn’t need to be much of a motive to tip the scale.
This is another tough one. As we said above, DDoS attacks seem to happen for a few reasons, so the answer to “why me” may be one or all of those reasons. A few factors do seem to contribute to why one site gets attacked more often, or more aggressively, than another:
- In times of elevated socio-political activity, such as wars, elections, coups, and economic collapse, traditional and social media sites are often targeted.
- Popular and controversial brands often see elevated numbers of attacks. These may be associated with perceived actions being taken (or not taken) by the company, competitive (thought this is uncommon), or personal grudge
- Attacks against cloud providers themselves (Google Cloud, Amazon Web Services, Microsoft Azure) seek to cause as much disruption as possible by disrupting those providers’ customers.
Sadly, in some cases there’s not much to be done to make attackers look elsewhere. It’s unlikely that your organization will change its business, or its posture, in order to avoid DDoS attacks. Of course there are many technical defenses that can be put in place, but aside from those, there are a few activities to avoid that could exacerbate things:
- Don’t deliberately taunt a particular community, especially a community known for “digital activism”.
- Don’t overcomplicate your site. This is a little technical, but the more “special” things your website does (personalization, dynamic features, chat, forms, polls, trackers, logins) the more difficult it will be to protect the site from attack, and consequently the more attractive your site will be to attackers. If you need those features, of course, use them, and Brightspot has a lot of them. But if you don’t need them, your page performance and your security team will thank you.
- Don’t make unnecessary claims about how secure and hacker-proof your site is, or how you have 100% uptime - even if you believe these things are true.
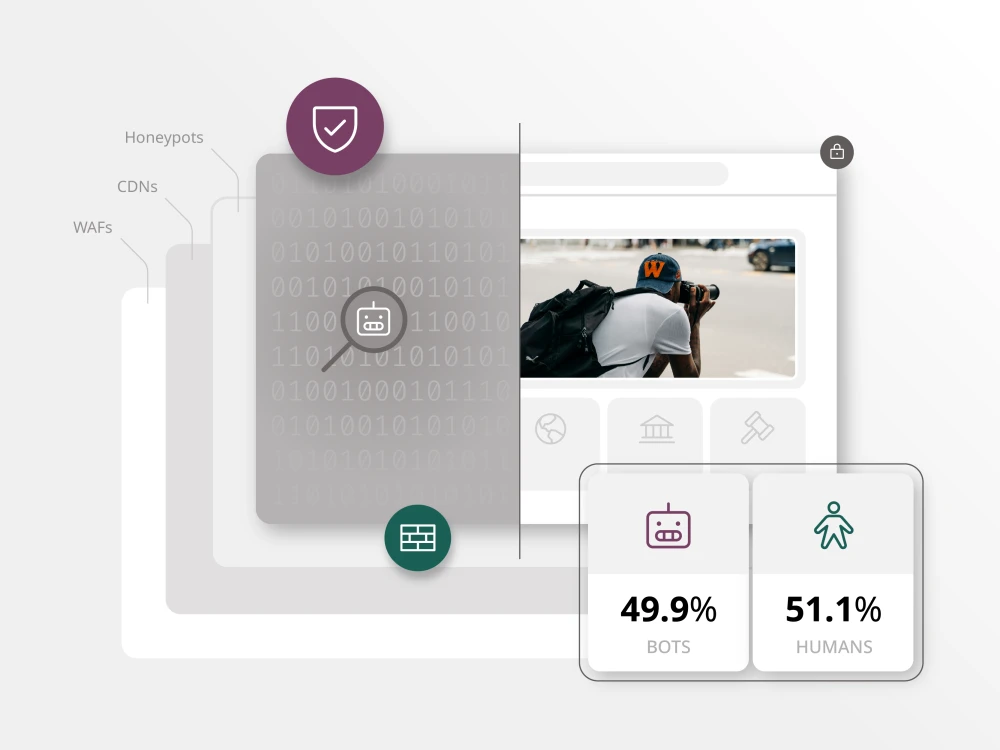
The sad fact is, DDoS attacks have become a part of what it means to do business on the internet. These attacks are difficult to predict, and can be frustrating—but there are various security tools that can help prevent, or mitigate, attacks that come your way.
David Habib is Brightspot’s Chief Privacy and Security Officer. Brightspot customers can schedule “office hours” with David to discuss this, or any, infosec topic.